Today I attended the ADTE Colloque 2016: The annual conference in Montreal (home for me) for a Quebec association with goals to promote free software in education.
Overall, the conference and its logistics were reasonably well organized; as far as the implementation of the event went, it seemed to go hitch free. Rooms that were appropriately sized were available, enough chairs were in place, there were no problems with the sign in, the microphones worked, the lunches arrived, and so on.
My interest was to see Richard Stallman, who was the keynote speaker.
Before he started his speech, I got to see his laptop almost closeup: He has a GNU sticker on it, an FSF sticker on it, and a small Trisquel sticker on it. I managed to ask him what the model was; an IBM Thinkpad X60, reconditioned, slightly upgraded, and marketed by a company called Gluglug.
Given that the conference was in French, Mr. Stallman presented what was no doubt his standard speech on free software, in French. (Let’s clear this up now: I’m a native English speaker, but Montreal is a predominantly French-speaking city; as such, since I live in Montreal, *of*course* I speak and understand French fluently.) Although I knew in advance that his French was competent enough to make his presentation in French, I was pleasantly surprised and very impressed that technically it was better than moderate in calibre, and that he could maintain it for over two hours with barely two or three requests to provide the French equivalent of a word or expression. And despite a fairly thick non-native speaker accent, it was almost surprisingly easy to follow.
His speech, although it appeared to be one of his standard speeches, went on too long in my view; 2.5 hours had been allotted for the presentation and questions, and I thought he could have accomplished the same thing in about 100 minutes, including questions.
I found that there were three downsides to his presentation:
– The “Church of Emacs” routine was off-topic or at least beyond the scope of the conference. Given what amounted to be a public audience, it was out of place. A cute parlour routine or pub talk in its own right, but out of place there.
– His comments about not having children were completely out of place, however legitimate they may be in their own right, and at best were poorly presented.
– Mr. Stallman apparently is losing his hearing, and asks people to speak a little more slowly, and clearly enunciate all their words. This is understandable, especially when those asking questions are not speaking his mother tongue; further, Quebec French and accents can be difficult even for native French speakers not accustomed to them. At one point, someone who forgot to speak extra clear and a bit more slowly elicited his ire as he either lost his temper, or whined like a child, repeating admittedly for the umpteenth time for the person to speak clearly and more slowly.
As for the rest of the conference:
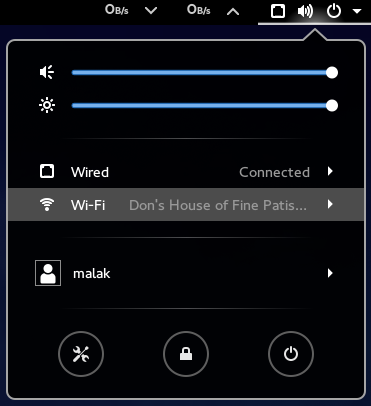
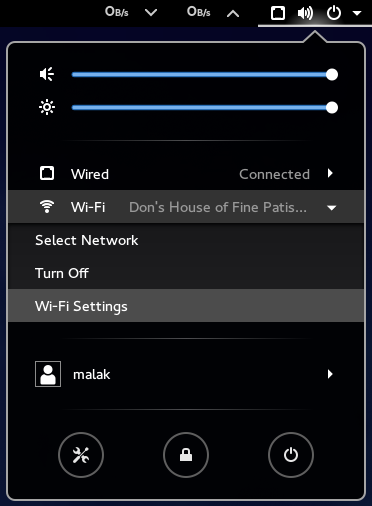
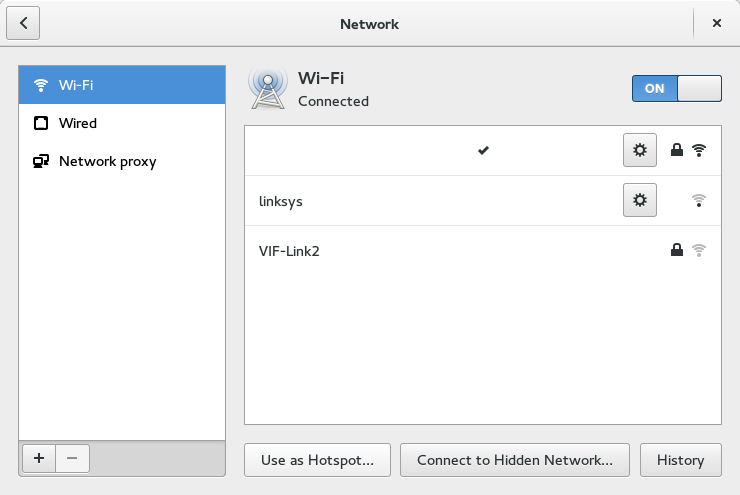
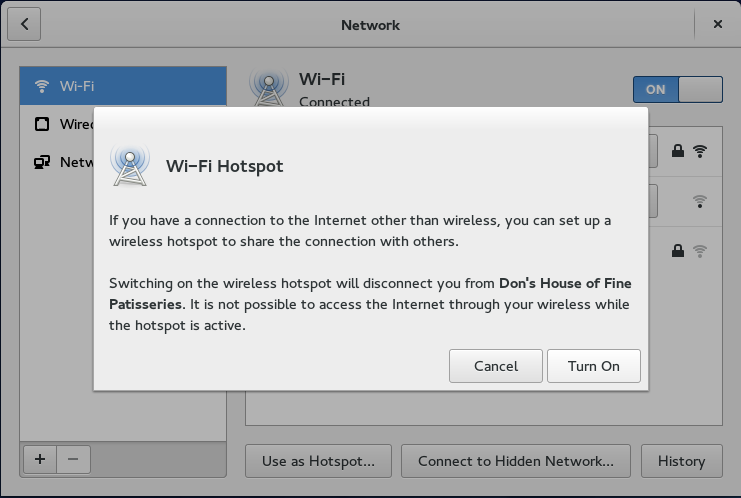
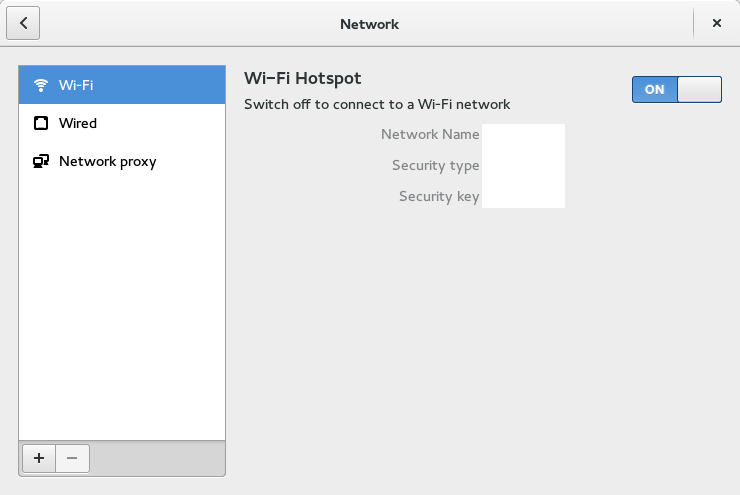
The overall conference had a few quirks. The iPads at the registration desks were funny and out of place, given the topic of the conference. The glaring and blatant use of a Microsoft Windows computer on the overhead projector was a weird oversight to the point of being shocking, regardless of the fact that for all intents and purposes it ended up only being used to display the wifi network and password, and one minor demonstration during a roundtable discussion. This was addressed in the first question period by an irate participant who venomously commented on it and expressed his feeling of being insulted, to the applause of roughly at least a third if not half the participants.
For me, the first round table, before Mr. Stallman’s speech, left something to be desired. I thought that they could have been better organized instead of being just “I’m Tom Smith and this is what I do. Oh, and this is what I know about free software.”
The second round table, after Mr. Stallman’s presentation, was a bit meatier and not quite as disappointing as the first. There was an IT person who was trying to slowly provide Free Software by placing it in their pool of software available to staff at his institution, alongside other software. Another panelist provided a good and enlightening response to a question, to the order of “Try explaining *that* to a powerful teachers’ union!”
My brother said the comments then as well as elsewhere in the day felt like we were still in 2006 instead of 2016 given their nature, such as:
– “Well GNU/Linux is hard to install” (I found it easy to install in 2008, and installing other software and fixing settings is something one does on any platform);
– “LibreOffice isn’t fully compatible with MS Word” (that’s a very nuanced conversation that strictly speaking is technically correct, but mostly trivially, IMO);
– “I’m accustomed to program X”;
– “I didn’t know that you could do that using free software”.
The lunch included in the admission fee was fine albeit a bit too frou-frou for my tastes, and totally inedible for my brother’s admittedly very narrow tastes. I would have hoped that there might have been more than three or four tables in the trade show part of the conference, which was held in the large lunch room area, but that’s neither here nor there.
The two afternoon sessions I attended were on the subject of “Accessing the Moodle Community”, and the ProjectLibre software.
The first presentation on the Moodle Community seemed a bit off and probably confusing to most of the participants, being a bit obscure and technical. However, once I re-read the title in the day’s schedule, I realized that it *was* on topic (both for the conference, and, on topic for his presentation.) Disappointingly, the presenter was delayed by a good fifteen minutes, for technical reasons: He could not use his computer for his presentation, given that for some reason he was unable to plug it into the projector. He then tried to present his slides prepared in LibreOffice with a computer using MS Powerpoint, which did not like his slides. He finally had to install LibreOffice on the supplied computer which was effectively permanently connected to the projector, or the setup otherwise effectively precluded the use of his own computer. He should have been prepared with the slides saved in PDF format, but to his credit he had placed the presentation online so that he could access it easily, in addition to having brought it on his computer.
The second presentation was a bit better as it at least was a demo of free software that can be used by educators / schools / etc. to either to manage their projects, what kind of software can be taught in schools, etc.
However, I thought that the two individual presenters I saw had two failings beyond what I mentioned earlier about the Moodle presenter:
– They only had about half an hour each; they could have done with at least another 15 minutes each. Each went over their allotted time; in any case, they should have timed things better in their presentations given that they knew of their time limitations, or should have known, given the announcements online and in the printed schedules liberally distributed during the conference.
– They should have been coached in advance with “ok, present what you want the way you want, *BUT*, please spend the first up to five minutes answering these five questions, such as a brief description of what the software / project / topic is, what its use could mean to the participants, etc. etc. etc.” In addition, I thought that each unfortunately were unprepared for people asking questions and making comments during the presentations, which could have been handled with “Could you wait until I finish my presentation, at which point I’d love to take your questions and feedback.”
Overall, however, I did love participating in the conference.
Update 27 April 2016:
Here is the link to the ADTE’s conference recap page (in French) (and here’s my archive)
In it are links to YouTube videos of Mr. Stallman’s presentation as well as a number of links to speakers’ quick resumé of what they spoke about to even sometimes slides of their presentations, again normally in French.